| - |

|
||||||||
| ||||||||
|
It is my great pleasure to offer my opinion on the issue of cyber security management based on my experience, to the general readers of IEICE Global Plaza, especially to younger researchers in Asia Pacific region where the cyber world has been drastically changing. As you know, the growth of the cyber world has continuously increased year by year. This is due to not only the continuously rising means of access to the door of the cyber world, but also the contents provided by cyber world which become much more varied and richer than before. Intel predicts that the number of networked devices will become twice as many as the global population this year, in 2017 there will be three times more connected devices than the people on the earth by 2017. The traffic of mobile communication which people tend to daily use will grow thirteen times in just five years by 2017. In term of contents, two years ago, they had only 30 hours of video contents being uploaded to YouTube per minute, today the volume of video contents has increased up to 100 hours of video contents per minute. They also had only around two million search queries in Google per minute two years ago, now the number of queries already reached 4.1 million. Values contained in the cyber world today are becoming richer and higher, consequently emerging threats continue to rise and lurk at the entrance and gateway into the world of cyber, transcend national boundaries, gender, ethnicity and age. Then, a unique convergence occurs because the union of global content flows to a local zone (a country) and vice versa, including the embedded threats following that. These cyber values also act as an accelerator for the growth of positive and negative sides of cyber world. Here, the cyber security depends on how to reduce the negative side effects, continuing to maintain the development of the positive side. It will be a good approach in effectively implementing and conducting the cyber security to know the current issues of the cyber security as follows. |
Embedded Threat The embedded threat is emerging cyber threats in networked devices or in applications because of some weakness since its birth. It comes out because of poor design and usually in form of a security flaw that exists without affecting the main functionality of devices. An example of this is the embedded threat in android devices where many security experts are concerned. Around 61 percent of all Android smart phones and tablets - or about 930 million devices - are running a version of Android that may contain known vulnerabilities which an attacker could remotely exploit to seize the control of the device or steal the data stored in it, according to the data security firm Rapid7 (See the details at http://www.bankinfosecurity.com/930-million-android-devices-at-risk-a-7784). This is because Google just announced that they would no longer update a critical component running on Android 4.3 "Jell Bean" and older devices. Another example is a finding from Check Point, a worldwide leading company in Internet security that released last December their finding of misfortune cookie, a critical vulnerability that would allow an intruder to remotely take over a residential gateway device and use it to attack the devices connected to it. This serious security vulnerability finding may affect at least 12 million leading-brand home and SME routers that appears to have gone unnoticed over a decade. This embedded threat issue is very important because usually it takes some time until it is recognized or found by hacker or security experts. Besides, when it is found, the devices could be already spread all over the world and it makes even difficult to patch the hole soon. Bigger problem may arise if hackers find it faster than its vendor or relevant security experts. Huge Digital Library The cyber world provides contents that are updated every second. Any type of information that we need now, mostly can be retrieved from the cyber world as long as we can access it. It looks like a free huge digital library. The positive issue about it is to make people smarter within a shorter time. On the other hand, the negative issue is that evil people find their solutions and tools easily. An experiment in UK explained how a seven years old primary school student just took less than 11 minutes to hack a public WiFi hotspot, by gaining the knowledge through searching online with 11 million results returned on Google and almost 14,000 video tutorials on YouTube. Data/Information Leak The leakage of data or information means factual incidents about how the cyber security still can be intruded. In 2014, so many industries, even IT based industries, were hit by data breach case. For example, the software maker Adobe was hit with 152 million records. Online marketplace eBay was drained of another 145 million. Around 36 million records have leaked almost every month last year so that no industry seemed unscathed. A huge digital library make attackers more creative, vulnerabilities existed in networked devices and applications are waiting to be exploited, this year it would not be difficult to predict that more data breach cases will appear. National ICT Development and Sustainability Most of countries now believe that ICT development is a must in their national development. It is because not only it can boost their economic growth but also it enables to catch up with other countries. The more connected a country is with ICT, the more connected it is to the cyber world. Its citizen not only becomes the citizen limited to his country's territorial border but also becomes one of 3 billion global cyber citizen. All of the cyber threats which globally existed include any kind of malware which automatically becomes their threat that lurk them anytime. To prevent the damage from any probable threat, any country should put and enhance their ICT development strategy together with its security consideration, especially reduce the risk in the weakest link so it can empower the security in a whole chain. Indonesia is one example of countries enhancing the cyber security strategy to maintain the national ICT development. Indonesia has faced a tremendous cyber threat as a part of the global cyber world from year to year, in line with its many improvements in ICT infrastructure. The improvement in broadband connectivity can be seen in the first quarter of 2014, the broadband adoption rate in Indonesia is very high, reaching 262 percent increase quarter over quarter. It is predicted that the growth will continue as an Indonesian telecommunications company already announced plans to pass 20 million homes on Indonesia's roughly 900 inhabited islands with 10Gbps down/2.5 Gb/s broadband services. Fig.1 shows the Internet growth rate in Indonesia that IIIEEEIIICCCEEE GGGlllooobbbaaalll PPPlllaaazzzaaa continuously has increased as the telecommunication and broadband access was better and better. The cyber security condition in Indonesia observed by ID-SIRTII/CC (Indonesia Security Incidents Response Team on Internet Infrastructure / Coordination Center) as Indonesian National CSIRT/CC team shows tremendous incidents indicated by number of attack traffic, malware activities, embedded threats on the Web, data 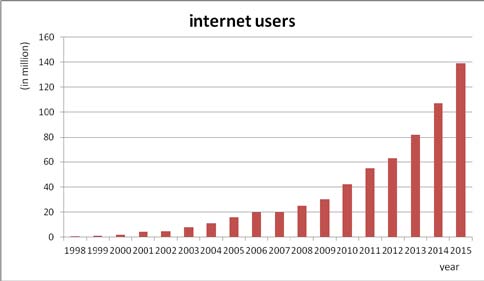 Fig.1 Continously increasing Indonesia Internet users. (source: Indonesia Internet Service Provider Association.). leak and Web defacement. In the first quarter of 2014, Indonesia even become one of the top rank three originating countries of global attack traffic monitored by Akamai (a cloud computing services and content delivery network provider in USA). The attack traffic within 2014 increase compared to 2013 was observed to be around 48.4 million attack traffics during the last one year where the port 22 became the most targeted port, different from 2013 when the volume of attacks targeting port 1434 was the biggest. Fig.2 shows incidents that have been monitored last year. The number of vulnerability cases increased 60 times that of the previous year, caused more Web defacement incidents in 2014. This vulnerability is an example of embedded threats mentioned earlier. To prevent serious damage from embedded threats, misuse of huge digital library content and leakage of important information, ID-SIRTII/CC continue to strengthen the security awareness massively at all levels every year. The activities consist of cyber monitoring, cyber research, socialization-education and international cooperation. Socialization-education activities are provided not only in its usual form such as giving free public training and workshop to the people who are responsible to network and IT in their organization but also in the form of incidents drill test and cyber national event, national or international competition and contest. The “National Internet Security Days”, an event initiated by ID-SIRTII, even enables to attract a hundred to thousand people to join. All of these activities are important because the cyber security relates to not only technical aspects but also non-technical aspects. We believe the increasing security awareness massively will bring a tremendous impact, especially when we want to reduce the threats coming from the weakest link.  Fig.2 2014 cyber security incidents in Indonesia The author, Dr. Rudi Lumanto has served Minister of Communications and Information Technology, Republic of Indonesia as the Senior Advisor till last October, accepted our request to talk his experience based vision of cyber security management, to the general readers of IEICE Global Plaza. This article will encourage many researchers, engineers, and students, especially younger generation in Asia Pacific region who are facing the same issues. He graduated from Chiba University, BS deg. in 1988, Nagaoka University of Technology, ME deg. in 1992 and University of Electro-Communications, PhD deg. in 2005. He served Minister of Agricultural Indonesia (2005-2009), Minister of Communication and Information Technology Indonesia (2009-2014) as each Senior Advisor and he was a member of Indonesia ICT Council. Currently, he serves ID-SIRTII/CC as the Chair. He also serves University of Indonesia as the lecturer and Graduate School for Computer Science, STMIK Nusa Mandiri, Jakarta. |
|||||||
| | Top | | ||||||||
|
||||||||
| The 2015 IEICE General Conference will be held at Ritsumeikan University, Biwako-Kusatsu Campus, in Kusatsu City twenty km East of JR Kyoto Station, on March 10-13, 2015. English Sessions provided in the Conference are: (1) Poster Presentation by 12 International Section Representatives This event will be organized by IEICE International Affairs Committee (IEICE-IAC) on the occasion of Annual All Sections Meeting where IEICE Board members, twelve International Section Representatives (ISR) and ten domestic Section Chairs annually gather and discuss the strategy and planning of IEICE’s global academic activities in collaboration. All the ISR’s will introduce their vision, organization, activities and expected collaborations. (2) Symposium Session BS-3 BS-3 entitled “Advanced Technologies in the Design, Management and Control for Future Innovative Communication Network” will be organized by IEICE Communications Society (Technical Committee on Network Systems) as well as former years. It provides a complete English Session during the four-days of the Conference, to accelerate the globalizing academic activities of IEICE by encouraging younger researchers, engineers and foreign scholars studying in Japan with international participants. 60 papers will be given in English there. The best papers will be awarded by the Society. |
||||||||
Let’s Join the International Conference | ||||||||
| The 2015 IEICE Information and Communication Technology Forum (ICTF2015) will be held in Manchester, UK on June 3-5, 2015. Your participation is most welcome. It will provide a number of technical tracks, workshops and keynote sessions covering the interests of IEICE members. See the details of the conference at http://www.ictf2015.ieice-europe.org. For any enquiry, please contact the Secretary at piotr.zwierzykowski@put.poznan.pl. | ||||||||
| | Top | | ||||||||
| ||||||||
|
IWSS -IEICE Communications Soc., in New Orleans, USA, on Mar. 9, 2015,http://wcnc2015.smartspectrum.net/ WDN-CN2015 -IEICE Communications Soc., in New Orleans, USA, on Mar. 9, 2015,http://www.icwdn.org/ ISMICT2015 -IEICE Communications Soc., in Hayama, Japan, on Mar. 24-26, 2015,http://isads2015.asia.edu.tw/ IBP2015 -IEICE Communications Soc., in Bali, Indonesia, on Apr. 23-25, 2015,http://www.ibp-conf.org/ ICTF2015 -I EICE Europe Section, IEICE Communications Soc., in Manchester, UK, on Jun. 3-5, 2015,http://www.ictf2015.ieice-europe.org OECC2015 -IEICE Communications Soc., in Shanghai, China, on Jun. 28-Jul. 2, 2015,http://www.oecc2015.sjtu.edu.cn/ APSITT2015 -IEICE Communications Soc., in Colombo, Sri Lanka, on Aug. 4-7, 2015,http://www.ieice.org/cs/in/APSITT/2015/cfp.html APCC2015 -IEICE Communications Soc., in Kyoto, Japan, on Oct. 14-16, 2015,http://www.apcc2015.ieice.org/cfp/index.html INTELEC2015 -IEICE Communications Soc., in Osaka, Japan, on Oct. 18-22, 2015,http://www.intelec2015.org/ |
||||||||
| | Top | | ||||||||
|
||||||||
| This issue is delivered also by a free mail magazine “IEICE Global Plaza Online” with updated news of interest for you. Please
contact Prof. Takahashi, TFIPP (Task Force for International Policy and Planning) at
global@ieice.org, if you need. Back numbers are available in archives at: http://www.ieice.org/eng/activities/ieice_global_plaza.html |
||||||||
Fig.1 Continously increasing Indonesia Internet users. (source: Indonesia Internet Service Provider Association.) |
||||||||
| | Top | | ||||||||
|
||||||||
| | BACK | |
|
(C) Copyright 2014
IEICE.All rights reserved. |